Enumeration
Given credentials
Username: OliviaPassword: ichliebedichPort scanning
$ nmap -sCV -T4 10.129.214.40Starting Nmap 7.94SVN ( https://nmap.org ) at 2026-04-08 07:40 CDTNmap scan report for 10.129.214.40Host is up (0.0033s latency).Not shown: 988 closed tcp ports (reset)PORT STATE SERVICE VERSION21/tcp open ftp Microsoft ftpd| ftp-syst:|_ SYST: Windows_NT53/tcp open domain Simple DNS Plus88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-08 19:40:11Z)135/tcp open msrpc Microsoft Windows RPC139/tcp open netbios-ssn Microsoft Windows netbios-ssn389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb0., Site: Default-First-Site-Name)445/tcp open microsoft-ds?464/tcp open kpasswd5?593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0636/tcp open tcpwrapped3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb0., Site: Default-First-Site-Name)3269/tcp open tcpwrappedService Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:| smb2-security-mode:| 3:1:1:|_ Message signing enabled and required| smb2-time:| date: 2026-04-08T19:40:12|_ start_date: N/A|_clock-skew: 7h00m00s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 16.29 secondsFrom this listed port, we know that the server is run on Active Directory. Trying to Enumerating using netexec.
┌─[sg-free-1]─[10.10.15.203]─[htb-mp-2897749@htb-l7hpcxj8do]─[~]└──╼ [★]$ nxc smb 10.129.20.200 -u Olivia -p 'ichliebedich' --shares
SMB 10.129.20.200 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:administrator.htb) (signing:True) (SMBv1:False)SMB 10.129.20.200 445 DC [+] administrator.htb\Olivia:ichliebedichSMB 10.129.20.200 445 DC [*] Enumerated sharesSMB 10.129.20.200 445 DC Share Permissions RemarkSMB 10.129.20.200 445 DC ----- ----------- ------SMB 10.129.20.200 445 DC ADMIN$ Remote AdminSMB 10.129.20.200 445 DC C$ Default shareSMB 10.129.20.200 445 DC IPC$ READ Remote IPCSMB 10.129.20.200 445 DC NETLOGON READ Logon server shareSMB 10.129.20.200 445 DC SYSVOL READ Logon server shareSeems user Olivia given 3 share, trying to enum bloodhound via nxc LDAP.
┌─[sg-free-1]─[10.10.15.203]─[htb-mp-2897749@htb-l7hpcxj8do]─[~]└──╼ [★]$ nxc ldap 10.129.20.200 -u Olivia -p 'ichliebedich' --bloodhound --collection All --dns-server 10.129.20.200SMB 10.129.20.200 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:administrator.htb) (signing:True) (SMBv1:False)LDAP 10.129.20.200 389 DC [+] administrator.htb\Olivia:ichliebedichLDAP 10.129.20.200 389 DC Resolved collection methods: trusts, acl, objectprops, rdp, dcom, container, psremote, session, group, localadminLDAP 10.129.20.200 389 DC Done in 00M 01SLDAP 10.129.20.200 389 DC Compressing output into /home/htb-mp-2897749/.nxc/logs/DC_10.129.20.200_2026-04-09_123834_bloodhound.zipOpen all json extracted into bloodhound web.
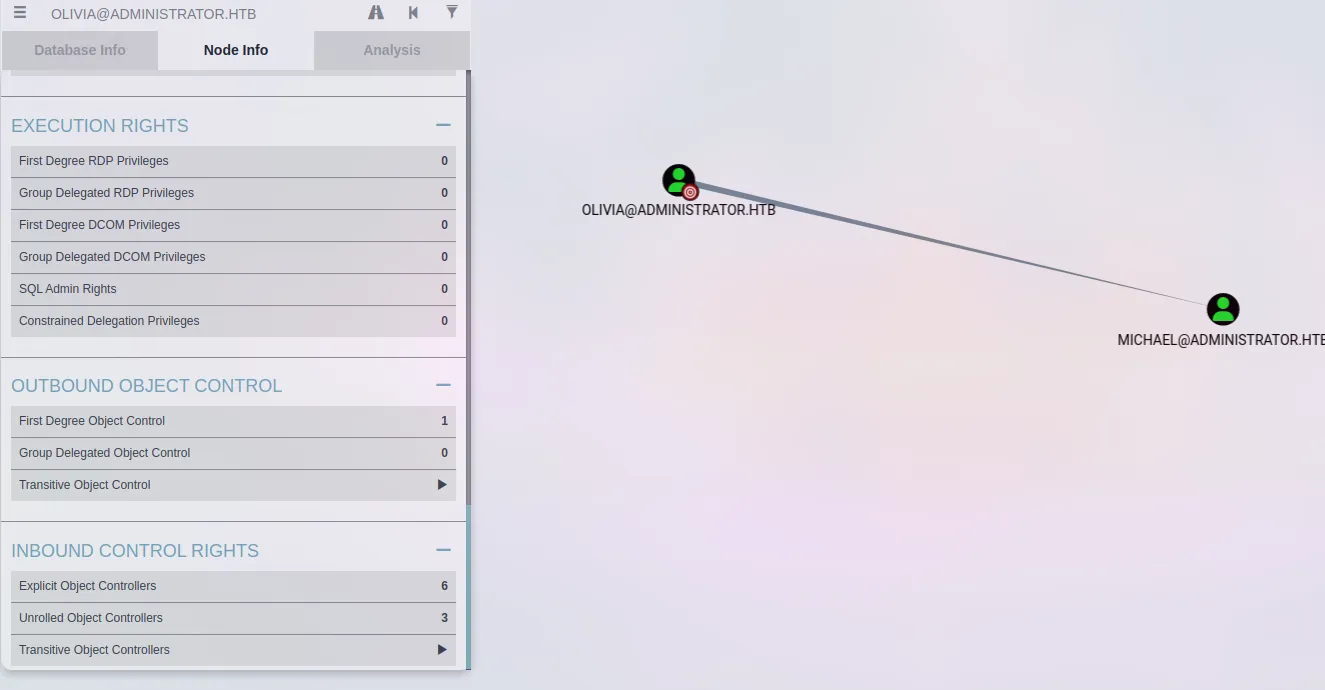
Seems olivia user have connection with michael.
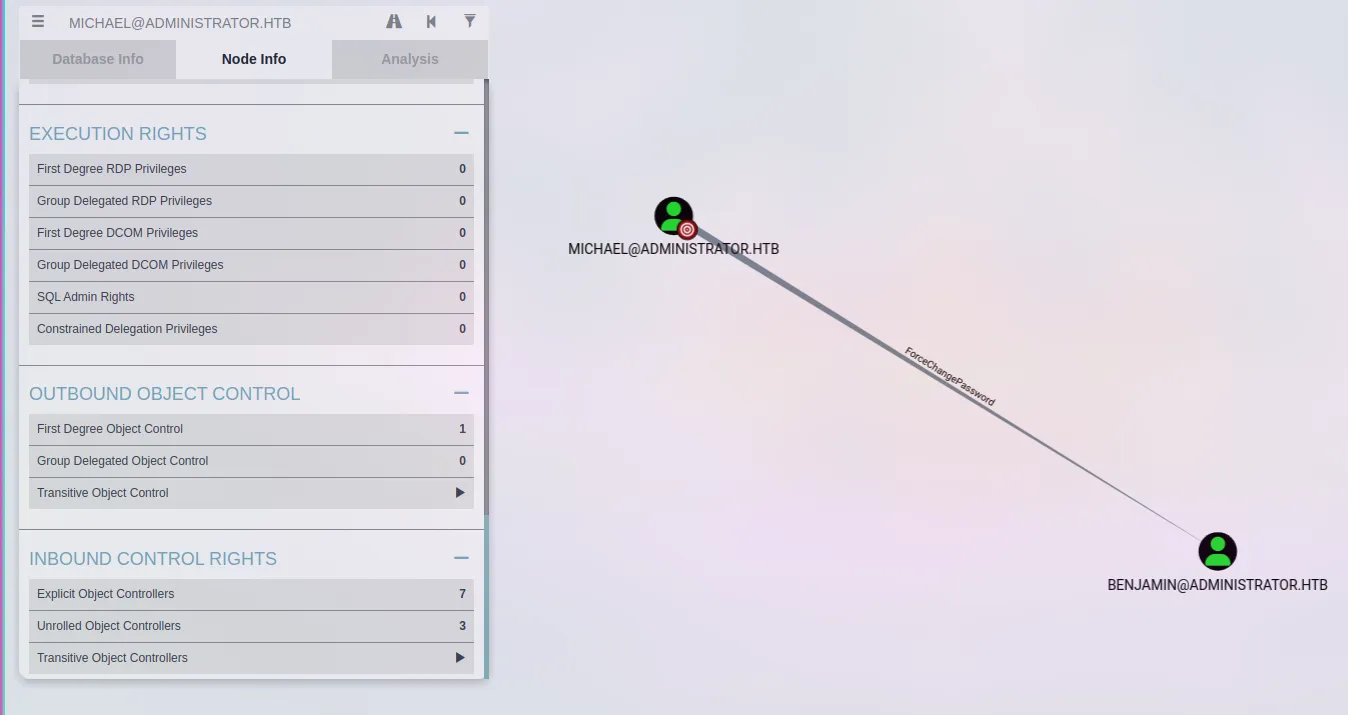
Michael have connection with benjamin.
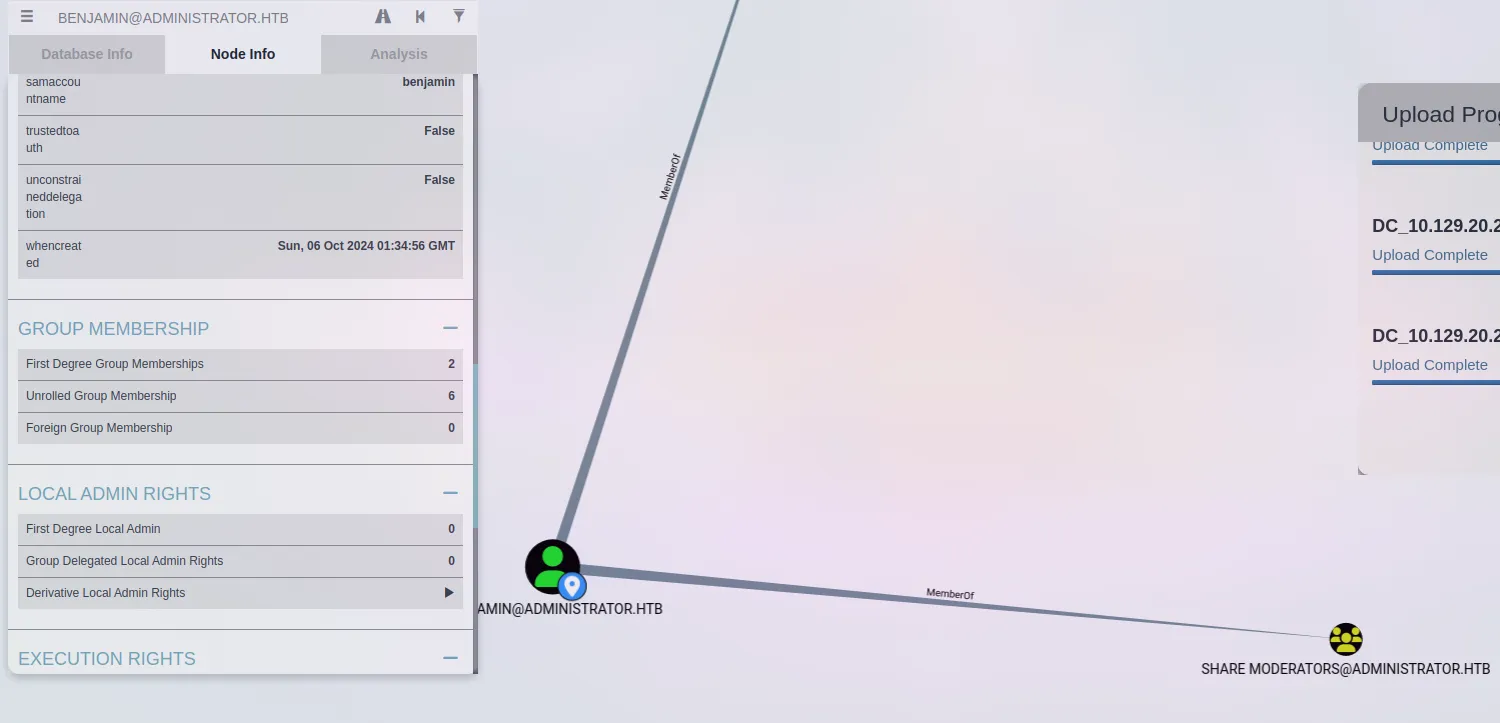
Benjamin users has joined non default group named share moderators.
To be continued